The Beyond Security Products You Know & Love
Black Box Fuzzing
BeSTORM
Get a scalable, cloud based, real-time black box fuzzer that doesn’t require source code and has over 250+ prebuilt protocol testing modules.
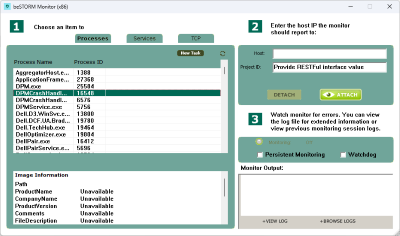
Detect real-time vulnerabilities without the need to access source code. Can help certify the security strength of any product, including IoT devices and automotive ECUs.
Vulnerability Management
BeSECURE is now part of Fortra VM
Fortra VM combines technology from Frontline VM and beSECURE to create an enterprise-grade vulnerability management offering that's powerful, scalable, and easy to use.
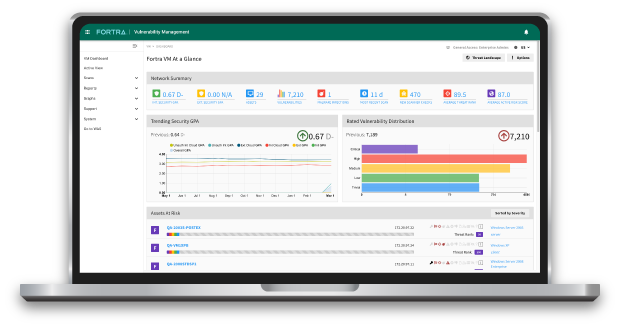
Our fast and accurate vulnerability management and assessment solution delivers cost effective network security scanning.
Get Started with Fortra
Implement a strategic, multi-layered defense that meets compliance requirements and safeguards your business against disruptive threats.