The average organization deploys more than 50 different security solutions to try to protect critical assets. Yet 51% of organizations surveyed have been breached via a cyberattack. This means that a strategy of buying and implementing defensive security solutions is not enough. Proactive security measures, such as penetration testing, must be employed as well.
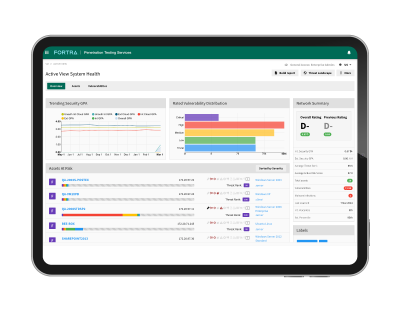
Fortra's Penetration Testing Experts are here to provide reliable security tests, from basic pen tests to complex engagements with sophisticated attack emulation. Our team will uncover security weaknesses and provide detailed suggestions on remediation.
Penetration Testing Service Offerings
What kind of penetration testing do you need? Internal, external, web application testing? Our team can work with your organization to discuss project scope and help determine what will meet your needs, from penetration tests to Red Team exercises.
Penetration Testing Services
Our pen testers will find and exploit vulnerabilities while challenging access controls in your infrastructure to get access to privileged systems and information in order to help determine and prioritize risk. IBMi platforms included.
Red Team Exercises & Application Security Testing
Red Team exercises fully simulate a cyber-attack scenario to help measure how effectively an organization can detect, defend, and withstand cyber threats by malicious actors. Our Red Teamers use all the industry leading tools and methods real hackers use to evade detection while discovering exploitable areas of the network, applications, credentials, and devices. Our red team can emulate internal attackers, external attackers, and can also tailor exercises for different objectives, including accessing sensitive information or gaining root control.
Application Security Testing consultants will evaluate the security of desktop, mobile, or web applications from an attacker’s perspective and are ideal for applications in development or prior to its latest release. These dynamic tests reveal errors in code as well as broken authentication or authorization while auditing the source code of your applications.
The Value of Third-Party Penetration Testing Services
Bringing in external consultants to test the security of your systems provides an objective, novel, and expert view of your security posture. Our team of experts provide a fresh perspective, tailoring each engagement to your needs to expose security weaknesses that may have been overlooked due to the on-site security team’s familiarity with the environment.
Whether you have internal pen testing, or have never put your organization to the test, our pen testers can provide new ways to improve your security, including increasing user awareness, finding new vulnerabilities, circumventing access controls, and finding unexplored paths to compromise high-value assets.
"When it comes to security projects, your team consistently delivers projects on time and on budget to keep us safe."
Web Application Developer
We can also offer assistance to internal pen testers, engaging in teaming exercises or providing third party verification of audits.
Scope Your Next Project
As cybersecurity breaches continue to threaten the stability of companies in every industry, it’s important to find the right vendor to perform a valid and beneficial assessment of your security. We understand every organization has unique security objectives and challenges, and we strive to tailor our services to meet your needs.