Fortra delivers comprehensive visibility and control over your data, eliminating blind spots and reducing risk. Our unified AI cybersecurity platform replaces fragmented tools with an integrated architecture that safeguards your data’s every move so your organization can work with confidence.
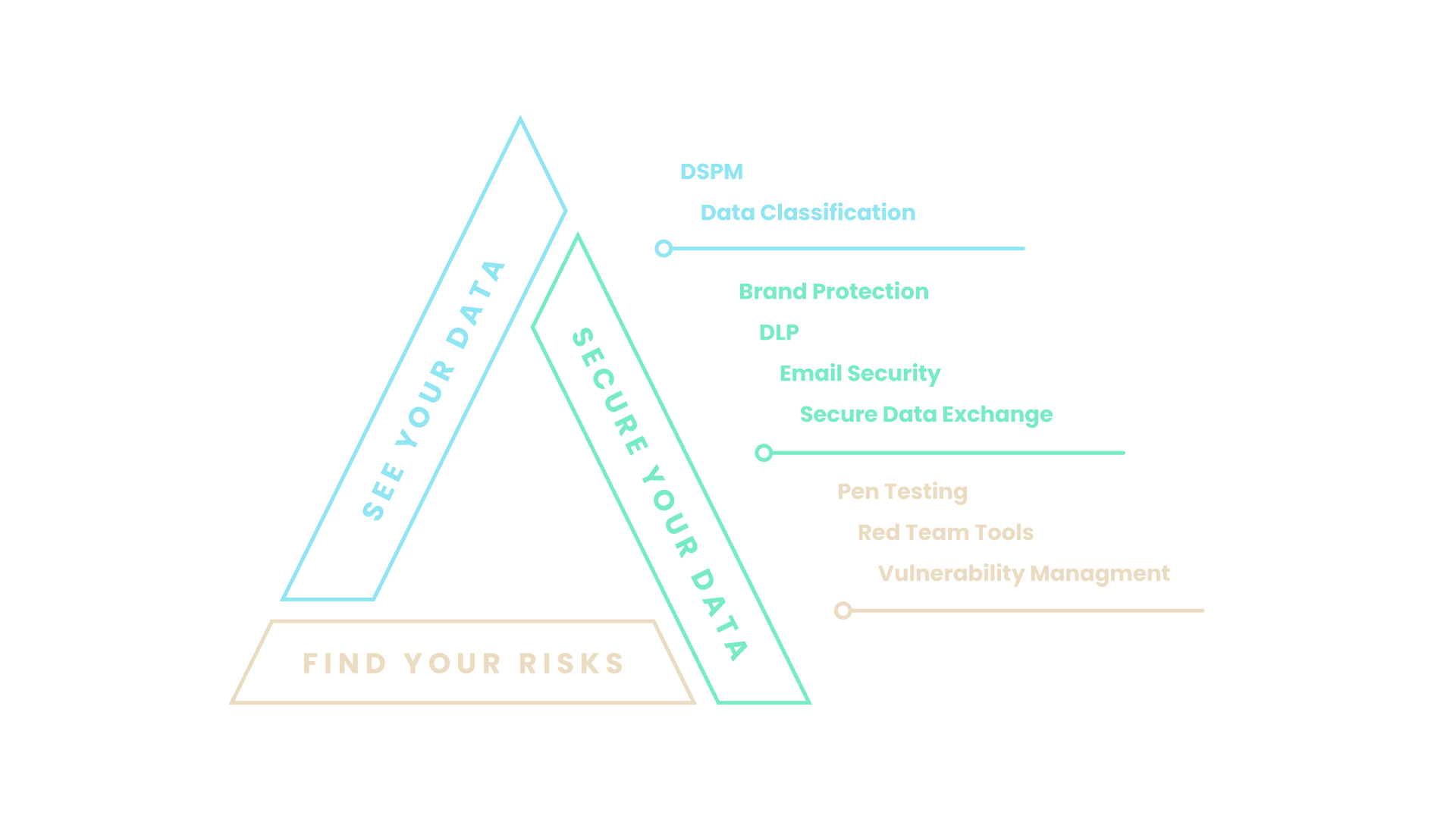
See Your Data. Secure Your Data. Find Your Risks.
See Your Data
Know your data so you can better protect it. Fortra enables complete visibility into your data: what it is, its sensitivity level, and where it lives. Discover and accurately classify all your data with AI-driven workflows. Integrated enterprise labeling leverages hundreds of built-in data types, with room to customize for your
organization’s unique needs.
Our Solutions: DSPM, Data Classification
Secure Your Data
Data security should enable innovation – not slow it down. Enforce unified policies across your entire data
environment, including endpoints, SaaS, cloud, email, and networks. Strengthen your posture further with
enterprise‑grade email security, online brand protection, and secure data exchange that streamlines the
compliant movement of sensitive data.
Our Solutions: Brand Protection, DLP, Email Security, and Secure Data Exchange
Find Your Risks
Quickly identify vulnerabilities, validate defenses, and reduce your organization’s risk. Fortra eliminates blind
spots by enabling security teams to find risks across their entire environment through penetration testing,
red‑team simulations, and vulnerability management. Intelligent sampling and deep‑scanning capabilities
strengthen discovery across every environment.
Our Solutions: Pen Testing, Red Teaming, and Vulnerability Management
How Fortra Helps
Complete Visibility
With full visibility, Fortra disrupts attacks before they succeed.
- Unified, cloud-native platform with agent
- Exclusive AI models for accuracy and automation
- Real-time indicators of compromise for changing threats
Flexible Delivery
Fortra offers data security tailored to organizational needs.
- Interoperable modules for any maturity level
- Product and/or managed services models
- Tiered packages and progressive discounting for superusers
Open Intelligence
Fortra anonymizes and correlates threats across our client base.
- Threat intelligence experts in diverse skillsets
- Bi-directional threat intel exchange with global law enforcement
- Exclusive threat research
- Third-party integrations
About Fortra
Fortra provides advanced offensive and defensive security solutions that delivery comprehensive protection across the cyber kill chain. With complete visibility across the attack chain, access to threat intelligence spanning the globe, and flexible solution delivery, Fortra customers can anticipate criminal behavior and strengthen their defenses in real time.