Cybercriminals are constantly refining their tactics to improve deliverability and increase the success of their campaigns. While email phishing remains one of the most persistent threats to organizations, many attacks now begin outside the inbox, using non-traditional lures or targeting users on platforms where they are more likely to engage.
For security teams, keeping pace with where threats originate and how they evolve can be difficult. New attack methods frequently emerge when criminals adapt techniques that have proven effective in other types of online fraud. In this blog, we explore three growing threat trends — QR code phishing, hybrid vishing, and the use of AI in cybercrime — and share practical ways organizations can defend against them.
QR Codes Delivered via Email
QR code abuse in email is one example where criminals use a successful attack tactic and replicate it in another space. QR phishing emails trick unsuspecting victims into scanning the code presented in the email body, causing them to land on fraudulent websites or download malware onto their devices. QR phish have increased in popularity due to their ability to bypass many security controls and a general lack of security awareness around their associated risks.
Enterprises have long faced risks from QR code phishing delivered via SMS, largely because these attacks occur outside the traditional corporate security environment. However, QR codes are increasingly appearing in email campaigns designed specifically to target corporate inboxes.
These threats remain difficult to detect and block. Many email security solutions still lack the capability to extract and analyze URLs embedded within QR codes, preventing them from properly inspecting the destination for malicious content. As a result, these messages may bypass standard phishing detection controls that would typically flag emails containing suspicious links or attachments.
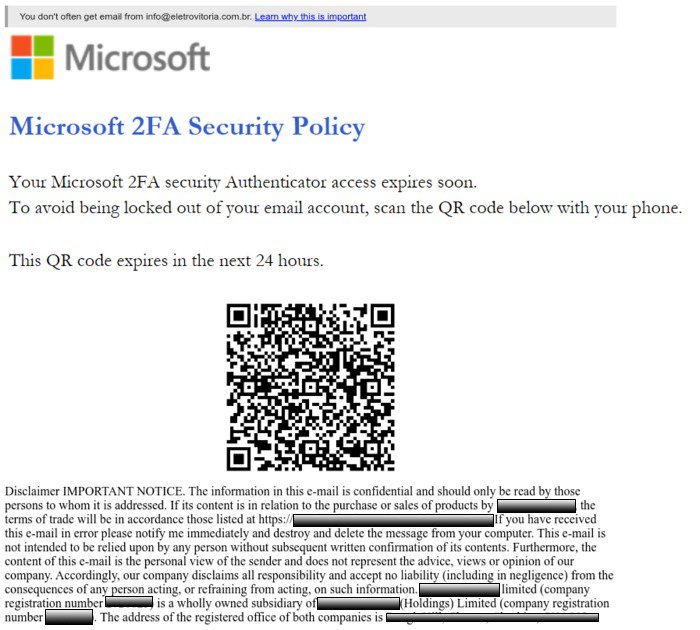
The move to incorporate QR codes into email is a perfect example of combining two familiar tools to mislead users. Email lures incorporating QR codes are the bridge between mobile and traditional email. Threat actors are taking advantage of how familiar the public has become with QR codes.”
In a large-scale phishing campaign detected by Fortra researchers, threat actors incorporated both QR codes and links in separate phishing emails to redirect victims to a phishing site, similar to A/B testing. The volume of phish detected using QR codes was more than three times greater than the phishing links.
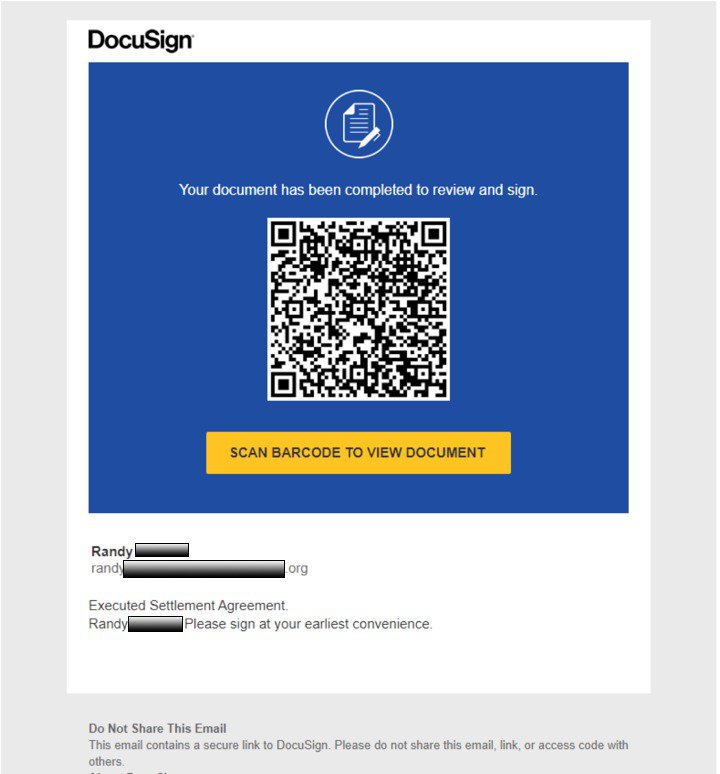
Failure to recognize a QR scam and subsequently scanning the code can result in stolen credentials, cash, or an infected device. In order to protect against these threats, security teams should focus on a combination of technology and employee reporting. One way to capture QR code threats is by implementing Optical Character Recognition (OCR). OCR is the process of detecting and extracting text from an image file, an image embedded within an electronic document, or a scan of a document and will fully inspect suspicious messages that make it into user inboxes. Additionally, employees should be trained to quickly report any suspicious emails.
Hybrid Vishing
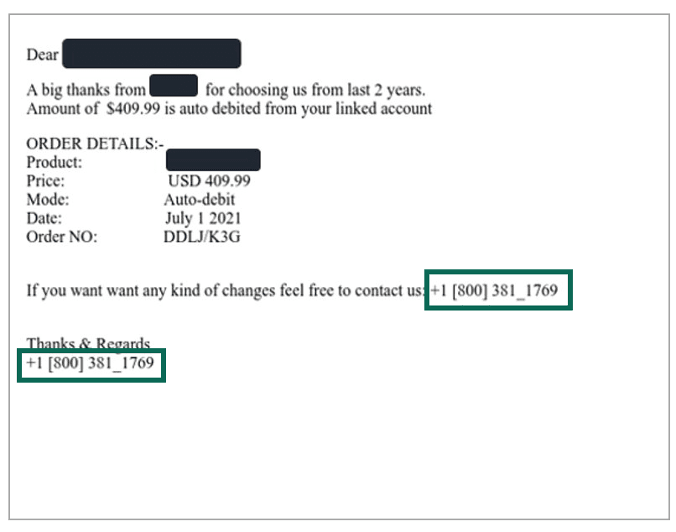
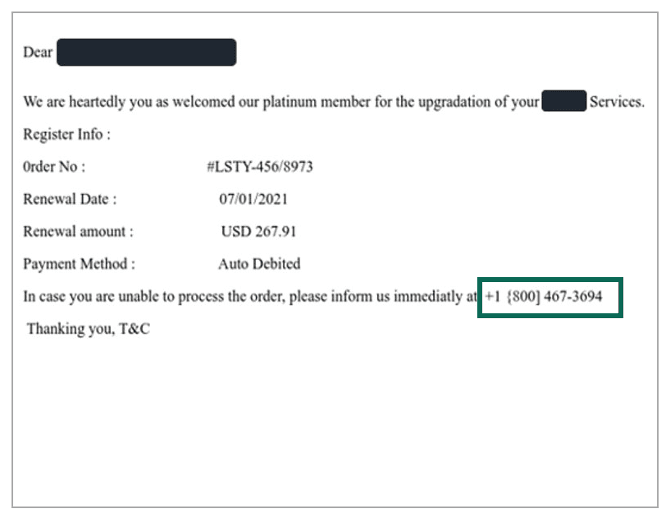
Phishing emails containing phone numbers, also known as hybrid vishing, have seen exponential growth over the past year, with reports of email lures containing phone numbers nearly doubling in 2022. These attacks often take the form of unexpected invoices, with telephone numbers as the primary point of contact.
Hybrid vishing attacks have continued to dominate response-based phishing reports in 2023, overtaking historical leader 419 scams, according to Fortra’s Suspicious Email Analysis. Most recently, hybrid vishing reports totaled nearly 40% of all response-based phish.
Much of the growth of hybrid vishing can be attributed to its ability to bypass email controls. Phone numbers can be much harder to block. As a result, we’re seeing an increase in phone numbers coming in both enterprise and consumer email-targeted attacks.
The top three ways criminals attempt to monetize hybrid vishing attacks are:
- ID Theft
- Credit Card Fraud
- Malware Implant
The challenges associated with hybrid vishing should be met with strong security awareness training and reporting capabilities. AI-generated lures will only add confusion to the legitimacy of email-based threats and education on how to identify these attacks should be prioritized.
Below are two examples of hybrid vishing attacks.
AI Application
AI continues to grow in sophistication, with government agencies issuing warnings about how deep fakes or AI-generated impersonation can be abused to target organizations. Disinformation campaigns are capable of occurring across a variety of channels, with both legitimate and illegitimate tools utilizing data science readily available to threat actors.
Fortra experts anticipate that in 2024 artificial intelligence will be increasingly weaponized in two spaces in particular: social media and email.
Social media
In 2023, attacks impersonating executives on social media surpassed those that targeted brands for the first time since reporting on this data. Many of these attacks have identifiers indicative of artificial intelligence and range from deepfakes to plagiarized images to AI-generated conversations. These attacks are increasingly sophisticated, with human-like traits that make it difficult for users and security controls to identify.
Social media has become a particularly attractive channel for AI-driven attacks, with roughly 60% of the global population active on at least one platform. Its role is also evolving, especially among younger users who increasingly rely on social platforms not just to communicate, but also to discover, research, and engage with brands.
Signs that AI may be used in social media scams often appear in the content itself. Repeated artistic styles across images, subtle visual anomalies, or objects that appear disproportionate to people in the scene can all indicate that imagery has been generated or manipulated using AI.
Generative AI will fuel more personalized email lures in the new year as bad actors increasingly use applications such as Chat GPT to produce grammatically correct text on demand, according to Fortra experts.
It’s no secret that average consumers have some level of personal data that’s exposed on the internet, whether it’s credentials we put into a platform that became compromised, or data we put on social profiles. Gone are the days you have an inheritance from a distant prince type of scam and enter the days of personalized lures that are going to be much more effective overall.
AI is also capable of creating polymorphic malware that evades security controls. Achieved through prompt engineering or, the process of modifying input to bypass content filters, ChatGPT can be used by even the most inexperienced actors to mutate code for advanced attacks. As large language models improve and consume more data, this has the potential to create AI threats only detectable by other AI models.
Looking Forward
QR code phishing, hybrid vishing, and the use of AI across social media and email are emerging as some of the most significant threats facing organizations. As AI-generated content and cross-channel attacks become increasingly common, organizations need a clear understanding of how these threats manifest and how they can lead to compromise.
To defend effectively, security teams should take a layered approach that combines broad threat detection, advanced technologies such as OCR and ongoing employee education to help users recognize and report suspicious activity.
