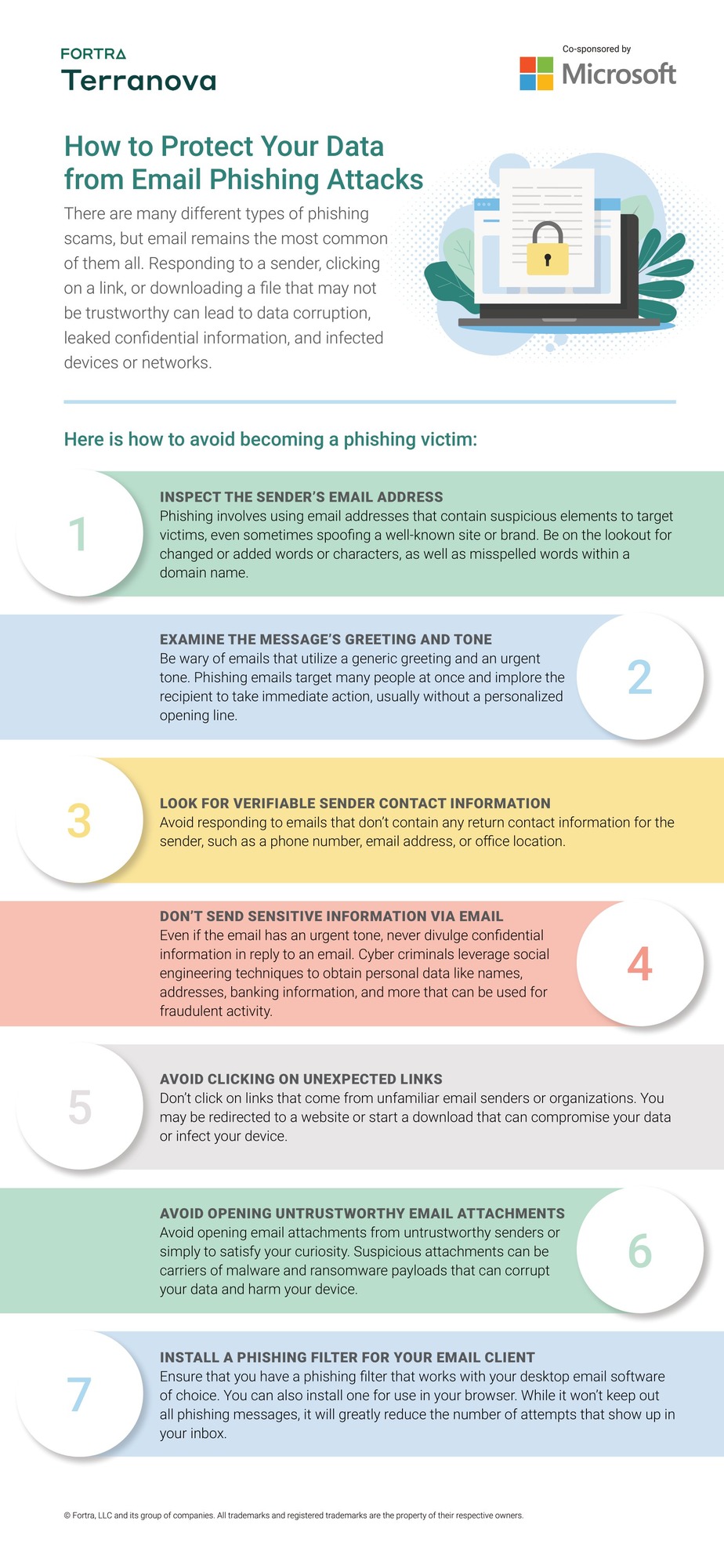
There are many different types of phishing scams, but email remains the most common of them all. Responding to a sender, clicking on a link, or downloading a file that may not be trustworthy can lead to data corruption, leaked confidential information, and infected devices or networks.
Off
Text
Text
How to avoid becoming a phishing victim
Phishing attacks are becoming more sophisticated and can appear in emails, websites, and messages. Staying alert is important, but using phishing prevention tools can also help by spotting and blocking threats before they reach you.
Text
1. Inspect the sender’s email address
Phishing emails often use addresses that appear to be real. Watch for small spelling mistakes, extra characters, or odd formatting that could mean the email is fake.
2. Examine the message’s greeting and tone
Be careful with emails that use general greetings and try to make you act quickly. If a message feels rushed and isn’t personal, it could be a phishing attempt sent to many people.
3. Look for verifiable sender contact information
Real companies usually include clear contact information. If an email doesn’t have a phone number, email address, or physical address, be cautious.
4. Don’t send sensitive information via email
Don’t share passwords, bank details, or personal information in response to an email, even if it seems urgent.
5. Avoid clicking on unexpected links
Links from people you don’t know can take you to fake websites or download harmful files. Always check where a link goes before you click it.
6. Avoid opening untrustworthy email attachments
Attachments from people you don’t know might have viruses or ransomware. Only open files if you trust the sender.
7. Install a phishing filter for your email client
Adding a phishing filter to your email or browser can help keep dangerous messages out of your inbox and give you extra protection.
95% of data breaches are due to human error.
Sign up for your 30-day phishing simulation free trial and help your organization avoid falling victim to a data breach.