Mobile App Protection: Prevent Brand Abuse
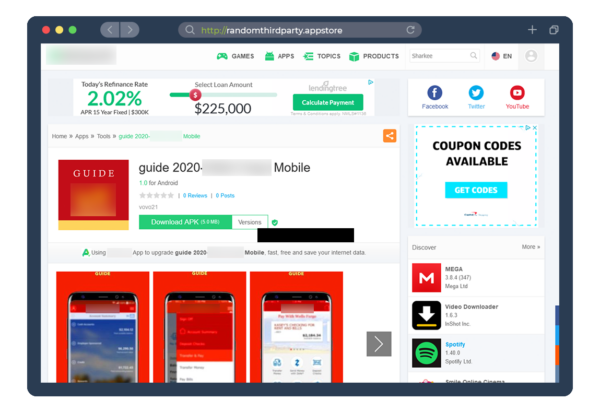
A fake mobile app hosted on a third-party store
Fake mobile apps impersonate trusted brands, infecting devices with malware that steals sensitive data. By mimicking the look and functionality of legitimate apps, these threats deceive users into installing and interacting with malicious content, leading to potential fraud, loss of trust, and brand damage.
Fortra Brand Protection takes down fake apps fast, safeguarding your customers and brand reputation with precision and speed.
Prevent Brand Abuse from Cloned Apps
As mobile apps become essential for socializing, business, and financial transactions, cybercriminals are exploiting users with fake and cloned apps. These malicious apps, often outdated and insecure, impersonate trusted brands using official logos and trademarks to trick users into downloading them, putting credentials and authentication codes at risk.
Fortra Brand Protection safeguards your brand by identifying and removing unauthorized clones, continuously monitoring hundreds of app stores, validating threats, and quickly mitigating abuse—protecting both your customers and your brand reputation.

Reduce Mobile Banking Trojan Fraud

Mobile apps are central to daily life, but cybercriminals exploit them with banking Trojans disguised as games or business apps. These Trojans activate when a legitimate banking app is opened, overlaying a fake login screen to capture credentials, then seamlessly return to the real app to avoid detection.
Fortra brand protection tools helps organizations combat credential theft by analyzing mobile malware and associated infrastructure. Our actionable threat intelligence strengthens authentication, prevents fraud, and protects both users and your brand.