For an outsider, it’s difficult to fathom what goes on in a SOC. It just looks like a mess of dashboards, screens, alerts, and stressed-out analysts. One might think that the SOC’s only purpose is to detect threats — but for those in the know, there’s much more to it than that.
Capacity management, escalation decisions, and explaining to the board why everything costs as much as it does are all part and parcel of daily life in a Security Operations Center. Running a SOC is about structure, skills, and making sure what you’ve built works for your organization. And that can be a serious challenge.
Skills and the Upskilling Challenge in 24/7 SOCs
Working as a SOC analyst is one of those jobs that requires you to constantly learn and relearn new skills and concepts. That’s the nature of cybersecurity — there's always a new tool to understand, a threat to thwart, a workflow to update.
But at the same time, the SOC itself never stops. If someone goes on training, your coverage won’t be as complete, and others have to absorb the load. In the short term, that’s manageable, but in the long term, fatigue can set in.
Therein lies the problem: a SOC must always evolve, but it can never pause.
For in-house teams, upskilling requires serious investment. Analysts must be given the opportunity to earn certifications, participate in labs and mentoring programs, and make use of protected learning time. That has financial and operational costs, but without it, skills stagnate, and investigations become reactive rather than strategic.
When you outsource a SOC, the vendor is responsible for skill development. It sounds simpler, but you’re not outsourcing accountability. You still need to ensure detections are being tuned, noise is reduced, and investigative depth is improving.
It’s easy to think of upskilling as purely a career development exercise — a perk of the job for your hardworking analysts. But upskilling is mutually beneficial; it directly impacts investigation quality. If your analysts can’t determine a root cause due to weak detection logic or poor log coverage, escalations become uncertain, and proving value becomes difficult.
Tiers and Escalations: Where Pressure Builds
Most SOCs are structured like a pyramid. Let’s break it down quickly:
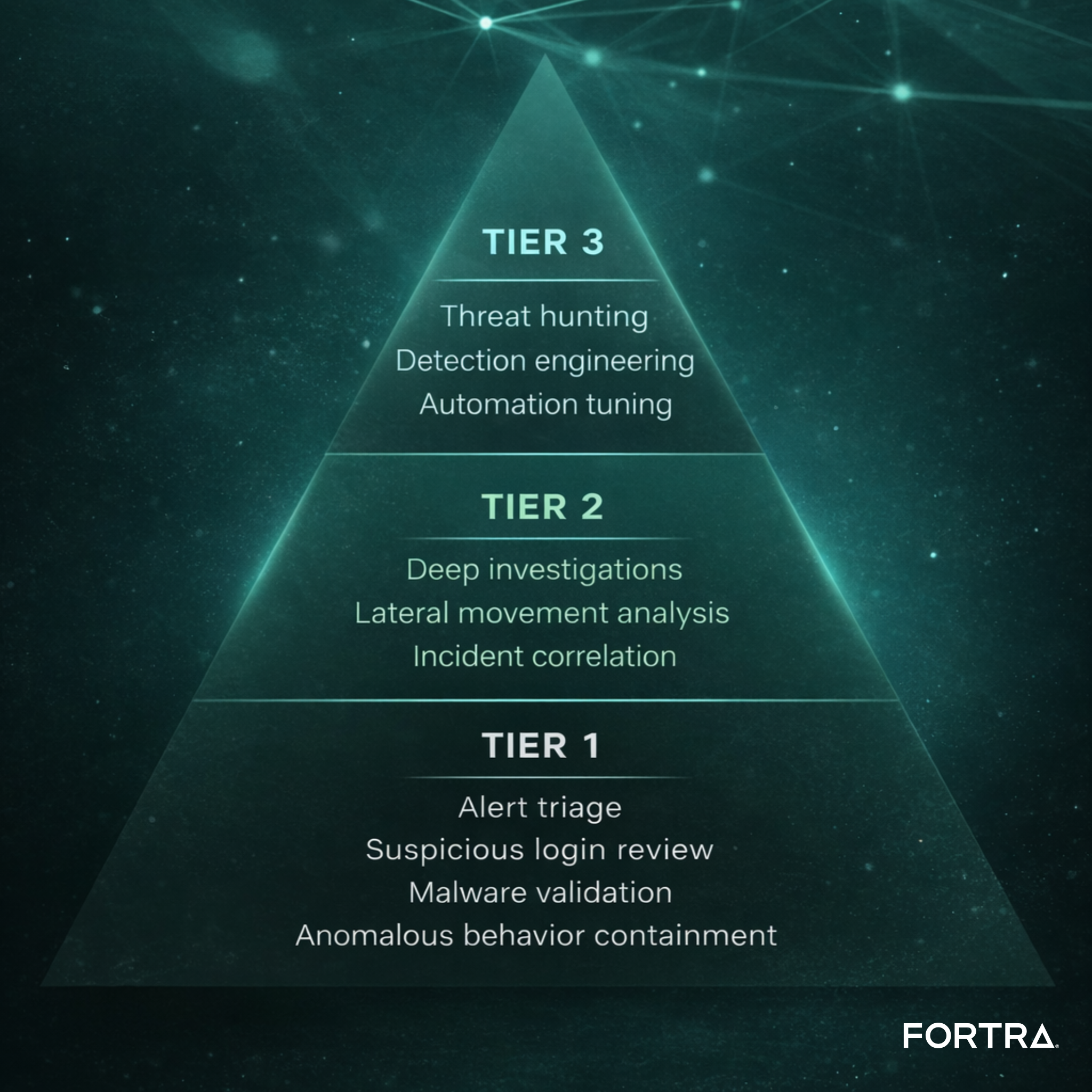
Few SOCs will struggle with defining tiers. Escalation, however, is a bigger problem. Escalate too quickly, and you overwhelm senior analysts. Too slowly, and risk lingers: the longer it takes an alert to reach more experienced staff, the longer the time between initial detection and response, and the more time attackers have to wreak havoc. If investigations stall because logs are missing or detections are poorly tuned, you’ve got a maturity issue.
Automation can relieve some of this pressure. You can triage repetitive, high-confidence alerts, at least in part, automatically. For example, you can group related alerts and isolate endpoints faster. But automation still requires continuous tuning – poor maintenance is just going to shift the workload elsewhere, not eliminate it.
Choosing the Right SOC Model for You
Not every organization should run the same type of SOC, and that’s a challenge in itself. But choosing the right model is simpler than one might expect.
Large enterprises and heavily regulated industries will typically maintain an in-house SOC. They need intimate knowledge of their own infrastructure, direct incident authority, and close alignment with IT and compliance teams. In these environments, outsourcing critical investigations may introduce more risk than it removes.
Mid-sized organizations tend to opt for hybrid models. They might outsource tier 1 monitoring to manage volume and cost, while tiers 2 and 3 remain internal to preserve investigative depth and authority. This can work well — but only if you clearly define shared responsibilities. If the vendor assumes you’re tuning detections and you assume they are, gaps are inevitable.
Smaller organizations may outsource fully. Running a 24/7 internal SOC can be financially unrealistic, and security may not be a core competency. In those cases, economies of scale make outsourcing practical.
The real challenge, however, is a mismatch.
If you build an in-house SOC without investing in skilled analysts, you’ll struggle. If you outsource without managing the relationship and reviewing KPIs, you won’t know whether it’s effective. If you buy advanced tooling without strong foundational controls — proper logging, retention, MFA, clear policies — investigations will stall before they even begin.
Bottom line? Your model must match your risk profile, budget, and governance structure.
Proving the SOC’s Worth
A big challenge for SOCs — and security teams in general — is that they are cost centers. They cost money, often a lot of it, and don’t generate revenue. That makes justification a major challenge and priority for SOC leaders.
The best way to overcome this hurdle is by understanding what senior leadership want to hear. They don’t care about tickets closed or alerts processed — they want to understand impact. When you’re presenting to the board, ensure you’re answering these questions:
How severe were the incidents?
How quickly were they contained?
Were you able to determine the root cause?
Is alert noise decreasing over time?
Are detections improving?
If you can’t explain why alerts spiked last quarter, you lack visibility. If you can’t identify initial access because your logs don’t go back far enough, you lack maturity. And if you can’t demonstrate continuous improvement, the SOC appears to be a static expense.
You should be able to tell a clear story about risk reduction, why escalation works, how skills are improving, how you’re tuning automation, and show that maturity is increasing over time.
The SOC: Expensive, But Necessary
Security controls can be expensive, and running a SOC can be challenging. But an incident can be catastrophic. You need to balance those realities in terms that the business understands. Because life in the SOC is about people, structure, governance, and constant evolution.
Your security strategy will live and die by whether your SOC is structured, skilled, and supported in a way that works for your business.
Disclaimer: The views and opinions expressed in this article are solely those of Zoe Rose.
